-
Hardware-Level Cryptography with Intel SGX: Securing the Untrusted World
Introduction In a world where malware, rootkits, and insider threats constantly evolve, traditional software-based security is no longer enough. Intel Software Guard Extensions (SGX) takes a different path — embedding cryptographic isolation directly into the processor. By creating a trusted execution environment (TEE) within the CPU, SGX allows sensitive code and data to run…
-
Dynamic Memory Analysis with AddressSanitizer at the Binary Level
Memory bugs are silent killers in software systems. They don’t just crash applications — they open doors for data corruption, undefined behavior, and exploitable security holes. Static analysis can help, but it’s often blind to runtime behavior. That’s where AddressSanitizer (ASan) comes in — a brutal, low-level memory checker that catches your mistakes as…
-
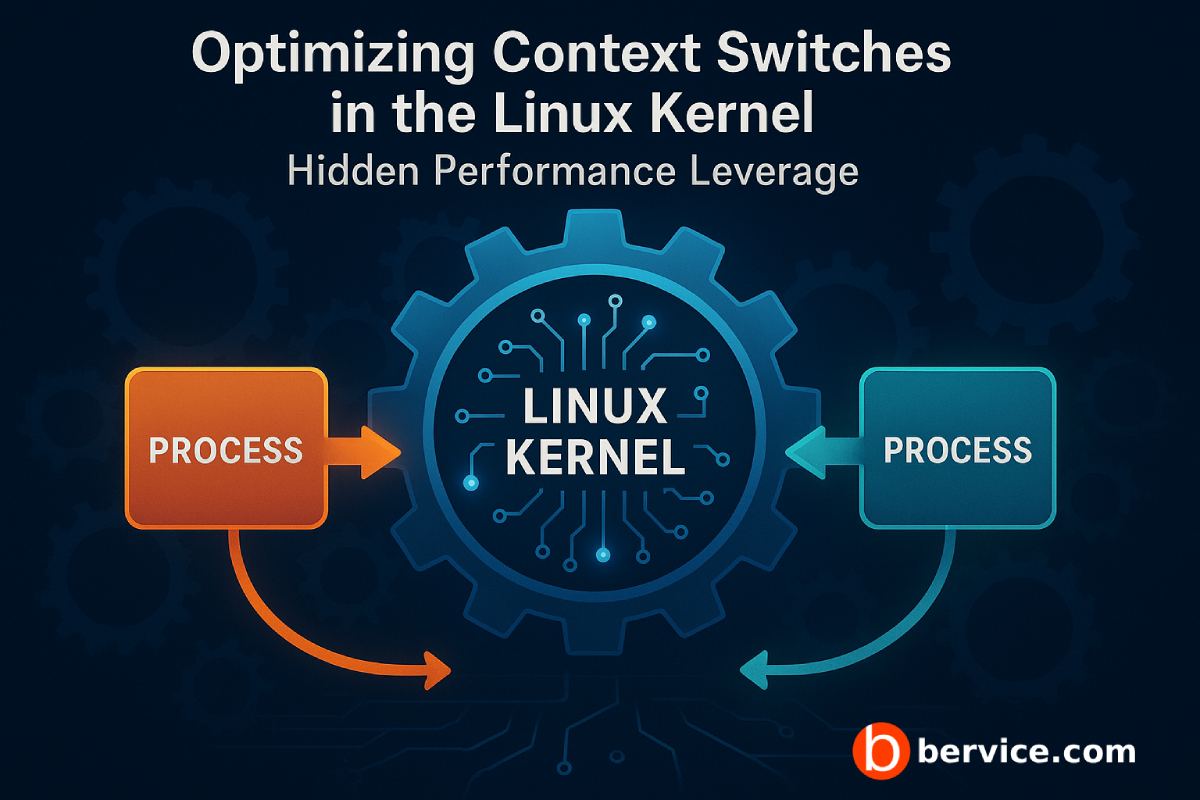
Optimizing Context Switches in the Linux Kernel: Hidden Performance Leverage
1. What Context Switching Really Costs Every time the kernel performs a context switch — moving execution from one thread to another — the CPU flushes registers, updates the program counter, and reloads process metadata. This is not “free multitasking.” It burns thousands of CPU cycles.When the switch rate spikes, cache locality is destroyed…
-

Hypervisor-level Exploits: Why VM Isolation Isn’t a Silver Bullet
Virtualization is everywhere: cloud providers, enterprise datacenters, developer laptops, CI runners. It looks safe — each workload sits in its own virtual machine (VM), separated by the hypervisor. That visual separation lulls engineers into false confidence. Here’s the blunt truth: if the hypervisor breaks, your isolation is meaningless. Hypervisor-level exploits (VM escape, hypervisor compromise,…
