-

Can Artificial Intelligence Trade in Financial Markets? Will It Eventually Make Market Decisions One-Sided?
Introduction Artificial Intelligence has rapidly transformed from an experimental technology into a powerful force influencing nearly every industry. Financial markets are among the sectors experiencing the most significant changes. Today, AI systems analyze vast amounts of market data, identify patterns invisible to human traders, execute transactions in milliseconds, and continuously adapt their strategies through…
-
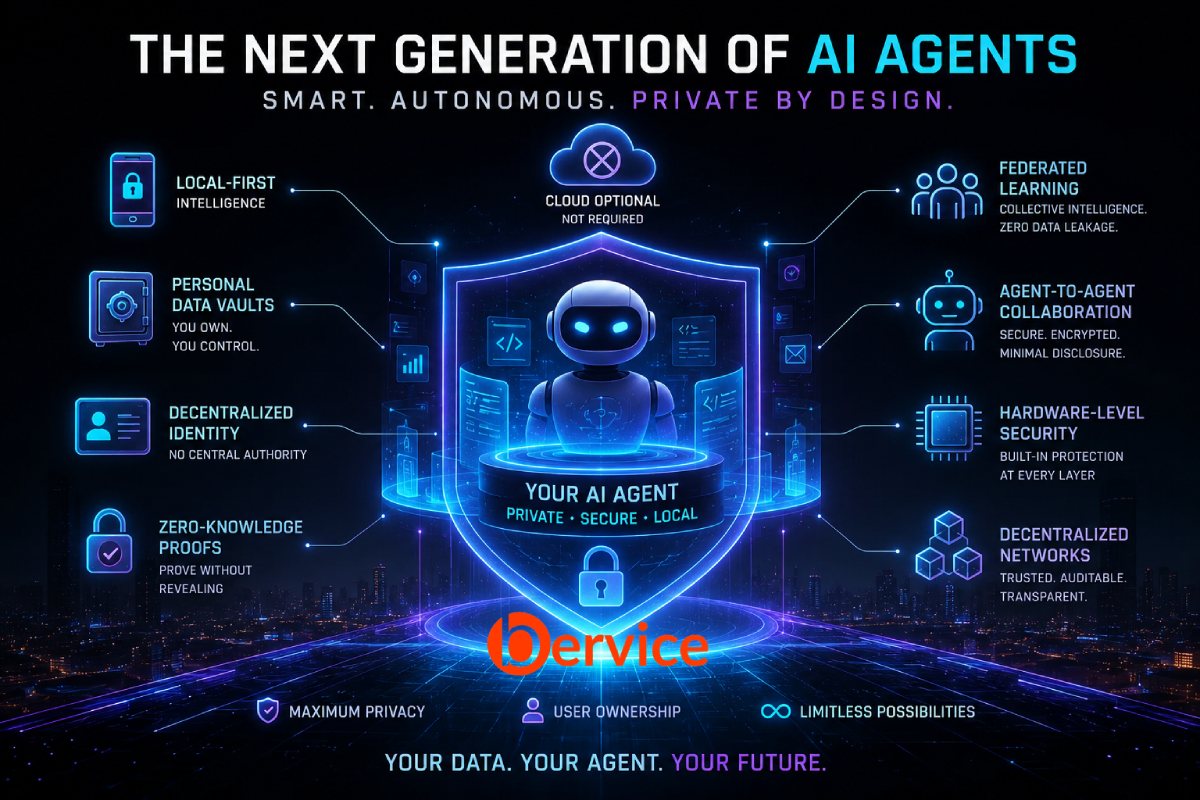
The Next Generation of AI Agents: Building a Future Where Privacy Comes First
Introduction Artificial Intelligence agents are rapidly evolving from simple assistants into autonomous digital entities capable of performing complex tasks on behalf of users. Today’s agents can schedule meetings, manage emails, conduct research, analyze data, and interact with various online services. However, as their capabilities grow, so do concerns about privacy, surveillance, data ownership, and…
-

How Local AI Models Can Work Together Like Puzzle Pieces Through Agent Systems
Introduction The future of artificial intelligence is not necessarily a world dominated by a single massive model. Instead, a more scalable, efficient, and intelligent future may emerge from thousands of specialized AI models working together like puzzle pieces. This concept is becoming increasingly important as organizations seek privacy, lower costs, faster performance, and greater…
-

Artificial Intelligence in Space: What Is Tesla Really Trying to Build?
1. The Next Frontier Is Not Just Space For decades, space exploration was mainly about rockets, astronauts, satellites, and national prestige. Today, the story is changing. The new space race is not only about reaching the Moon or Mars. It is about building intelligent systems that can operate beyond Earth with limited human control.…
-

The Future of Small LLMs Connected Through Agents: One Giant Model or an Army of Specialized Models?
Introduction: The Next Shift in AI Power The future of artificial intelligence may not belong only to the largest language models. For the last few years, the industry has focused heavily on building bigger models with more parameters, more training data, and broader general intelligence. Large LLMs have shown impressive reasoning, writing, coding, and…