-
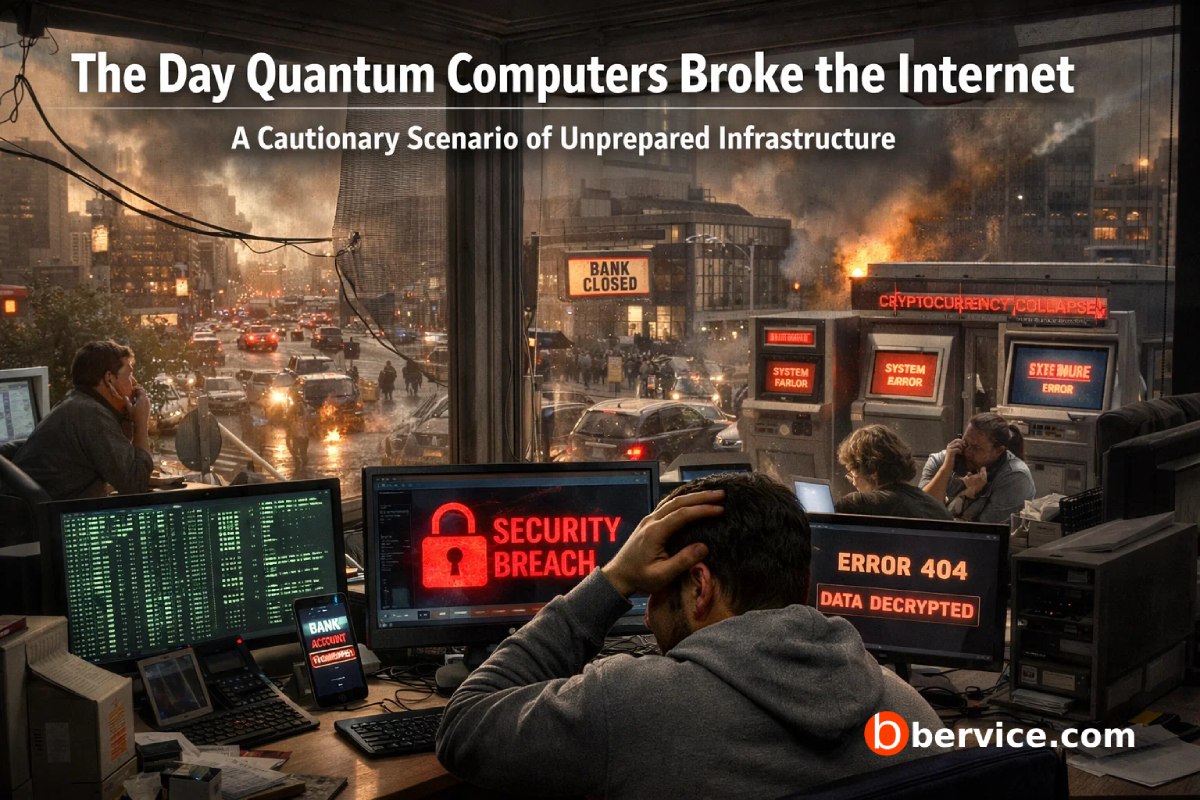
The Day Quantum Computers Broke the Internet
A Cautionary Scenario of Unprepared Infrastructure Prologue: The Morning Nothing Failed The day began quietly. No alarms. No warnings. Banks opened. Hospitals ran. Governments logged in.Every system reported green. Somewhere else, far from public dashboards and compliance reports, the first large scale fault tolerant quantum computer finished a calculation that classical machines would need…
-

What Is NIST? Its Mission and Its Role in the Post-Quantum Cryptography Transition
Introduction As digital systems become more interconnected and long-lived, cryptography has shifted from being a purely technical concern to a matter of national infrastructure and global trust. One organization has played a central role in shaping how cryptography is standardized and adopted worldwide: National Institute of Standards and Technology, commonly known as NIST. In…
-

Are companies ready for post quantum cryptography in 2026
In early 2026, many organizations are aware of post quantum cryptography, but most are not fully transitioned. The common situation is: planning has started, pilots are happening, and inventories are being built, while broad production rollout is still limited to specific parts of the stack like web traffic at large CDNs or selected cloud…
-

A Major Transformation in Cybersecurity Post Quantum Cryptography
Introduction The rapid advancement of quantum computing is reshaping the landscape of cybersecurity. While large-scale, fault-tolerant quantum computers are not yet widely available, their eventual emergence poses a serious threat to many of today’s cryptographic systems. Algorithms such as RSA, ECC, and Diffie–Hellman, which underpin global digital security, are vulnerable to quantum attacks most…
-

Malvertising How Cybercriminals Exploit Trust to Steal User Data
In recent years, cybercriminals have significantly refined their tactics to deceive users. Rather than relying on crude scams or obvious malware, attackers now invest time and resources into analyzing emerging technologies, user behavior, and legitimate digital ecosystems. Their goal is simple but dangerous: blend malicious activity seamlessly into everyday online experiences. According to a…